Information Security in the US Firearm Industry
Lessons from Past Breaches, Compliance Imperatives, and Emerging Threats
Who’s This Article For?
Executives, and IT Workers of US Firearm manufacturers, Stakeholders, and people with general interest in the US Firearm industry in ways to strengthen their cybersecurity posture.
Also to mention you contact me anytime with any questions/comments through the buttons immediately below, and at the end of this article.
I’m also available to be hired as a consultant for your company.
My Background:
20+ years experience in the IT industry
10+ years experience working in the US Defense Industrial Base (DIB)
Former Head of Cybersecurity at Geissele Automatics/Gwynedd Manufacturing
Former Head of Cybersecurity at (Unnamed) Robotic Dog manufacturer
Current Information Security Director at (Unnamed) large Construction company
5+ years working in CMMC compliance
Certifications
The United States Firearm Industry
The firearm industry operates at the intersection of national security, consumer privacy, and high-stakes manufacturing. Firearm and ammunition manufacturers, along with their suppliers, retailers, and ranges, handle sensitive technical data, customer personally identifiable information (PII), and regulated defense articles. A single cyber incident can expose gun owners to physical risks, leak proprietary designs, disrupt production lines or trigger regulatory violations with multimillion-dollar fines. As the sector adopts smart manufacturing, cloud services, and connected systems, cybersecurity has evolved from a back-office concern into a core business and compliance requirement.
This article examines notable past breaches affecting manufacturers and retailers, persistent current vulnerabilities, key compliance obligations (especially ITAR), and the threat vectors likely to intensify in 2026 and beyond. Whether you run a major manufacturer like Smith & Wesson or a specialized parts supplier, these insights provide actionable context for strengthening defenses.
The most recent detailed ATF Annual Firearms Manufacturing and Export Report (AFMER) covers 2023 data (released with the standard one-year lag; 2024/2025 full figures expected in 2026–2027). Key highlights:
Total domestic firearm production: 8,466,729 units (down 15.4% from 2022).
Top 5 U.S. manufacturers by 2023 production volume:
Sturm, Ruger & Co. — 1,304,628 firearms
SIG Sauer — ~1,001,916 firearms
Smith & Wesson Brands — 991,565 firearms
Savage Arms — 725,644 firearms
Henry Repeating Arms — ~404,849 firearms
Palmetto State Armory and other high-volume AR-platform makers also remained significant players.
The Complete Gun Manufacturer’s List (2026) via Ammo.com
Past Data Breaches: Studying the Past to prepare for the Future
The firearm sector has experienced a mix of direct cyberattacks, accidental exposures, and controversial data-handling practices. While large-scale manufacturer breaches remain less publicized than those in retail or government, several incidents highlight systemic risks.
Smith & Wesson Magecart Skimmer Attack (November 2019): Hackers injected malicious JavaScript into the company’s online store checkout page. The skimmer captured customers’ payment card details, names, and addresses in real time before the data reached legitimate payment processors. The compromise lasted days before discovery and removal. This classic supply-chain-style web attack underscored the dangers of unpatched e-commerce platforms in an industry where customers expect high privacy.
Guns.com Breach (January 2021): The firearms retailer suffered a sophisticated attack exposing approximately 376,000 unique email addresses plus names, phone numbers, physical addresses, gun purchase histories, partial credit card data, dates of birth, and bcrypt-hashed passwords. The breach was not primarily designed for data theft but caused operational disruption; however, the exfiltrated PII created long-term identity-theft and doxxing risks for gun owners.
Saeilo Enterprises / Kahr Arms Ransomware (August 2024): The parent company of Kahr Arms, Magnum Research, Tommy Gun, and Thompson/Auto-Ordnance was hit by the Metaencryptor ransomware group. Attackers claimed 11.5 GB of data. Saeilo notified 8,725 individuals that their names, addresses, driver’s licenses, and other PII had been compromised. The incident affected servers across multiple brands, illustrating how ransomware can cascade through corporate families.
Mister Guns Ransomware (November 2025): Texas-based firearms retailer and gunsmith Mister Guns was compromised by the SECUROTROP group, which exfiltrated 290 GB of internal documents, customer records, financial data, transaction histories, and operational files. The company later notified 21,225 individuals (including 19,662 Texans) that exposed data included full names, Social Security numbers, dates of birth, driver’s license numbers, concealed-carry licenses, passports, military IDs, and biometric fingerprint files in some cases. The breach combined ransomware disruption with high-risk PII exposure.
Other notable incidents include the 2023 compromise of CMMG (listed by the BlackCat/ALPHV ransomware group) and earlier UK cases such as Guntrader (2021) and the National Smallbore Rifle Association (2023), where customer gun-owner data appeared on the dark web.
Beyond technical breaches, the 2024 ProPublica investigation revealed that at least ten major manufacturers—including Glock, Smith & Wesson, Remington, Marlin, and Mossberg—quietly supplied hundreds of thousands of customer names, addresses, and purchase details to the National Shooting Sports Foundation (NSSF). The NSSF used this data for political mobilization via programs like GunVote and even shared subsets with Cambridge Analytica. While not a “hack,” this unauthorized sharing eroded trust and sparked 2025 calls for federal inquiries by gun-owner advocacy groups.
Government-linked exposures provide additional context: California’s DOJ accidentally published concealed-carry permit data for nearly 200,000 individuals in 2022, and Canada’s Firearms Program suffered a 2021 malware incident exposing 2.2 million records—the largest federal breach in five years at the time.
These events demonstrate that attackers target both technical vulnerabilities and the unique sensitivity of firearm-related data.
Current Issues: Persistent Vulnerabilities in the Firearm Ecosystem
Today’s challenges extend far beyond isolated breaches:
Ransomware as a Business-Disruption Weapon: Manufacturing is a prime target (17% of attacks in 2025 per some threat reports). Groups prioritize operational technology (OT) and industrial control systems (ICS) to halt production lines rather than just encrypt files. Firearm manufacturers’ reliance on CNC machines, inventory systems, and just-in-time supply chains makes downtime especially costly.
Website and E-Commerce Risks: Magecart-style skimmers and third-party tracking scripts remain common. Smith & Wesson faced a 2025 class-action lawsuit alleging that its site continued transmitting user data to trackers (Google, X, etc.) even after users selected “Reject All” cookies, violating privacy policies and California law.
Privacy and Data-Sharing Practices: The NSSF scandal highlighted how warranty cards, dealer records, and loyalty programs create massive customer databases that can be repurposed—or leaked.
Supply-Chain and Third-Party Exposure: Vendors, cloud providers, mailing services, and even cybersecurity tools themselves have been compromise vectors. A single weak link (as seen in the Canadian program’s third-party mailing vendor) can expose millions of records.
How Can We Solve this?
Focus on The Basics
Lets focus on the basics. Without getting the basics right you can’t do the high level stuff you may have to do.
What are the Basics?
People, Process, Technology
Who are your employees (including subcontractors, associates, etc)
How do our people work?
What software, hardware do they use?
People
Who are your employees (including subcontractors, associates, etc)?
Do we have a list of all employees?
Do employees have their own devices?
Do employees have their own log in credentials?
Physical Protection
Check all exterior doors for your building(s).
Do they close and open properly ?
Do we use keycards or pins to get into the building?
Do we have cameras installed on all entry and exits points?
Is the data backed up as needed?
Process
How do our people work?
Do they work in office?
Do they travel?
Do we know what normal traffic looks like?
Where do our endpoints log in from?
Do we have a count of our endpoints?
Technology
What software, hardware do they use?
Can we control what goes on our endpoints?
Do we perform daily scans?
Do we have a VPN that’s always on?
What software do our employees use daily?
If we look at the top three initial root access exploit methods their almost always the same:
Social Engineering (phishing, vishing, smishing, etc)
RDP Attacks (from unpatched/unmanaged devices)
Unpatched Software (vulnerabilities left exposed too long)
So starting at the basics listed above helps to protect against these three threat vectors.
Compliance: ITAR, CMMC, and Data-Protection Mandates
ITAR
Firearm manufacturers are subject to some of the strictest regulatory frameworks in U.S. industry. International Traffic in Arms Regulations (ITAR): Firearms, ammunition, and related technical data fall under Category I (Firearms, Close Assault Weapons and Combat Shotguns) and Category III (Ammunition/Ordnance) of the U.S. Munitions List (USML). Any company that manufactures, exports, or brokers these items—or handles their technical data—must:
Register annually with the Directorate of Defense Trade Controls (DDTC).
Implement strict access controls so that only U.S. persons (with narrow exceptions) can view ITAR-controlled data.
Obtain export licenses (e.g., DSP-5) before sharing technical data, drawings, or software with foreign persons, even inside the United States.
Maintain records and audit trails for any transfer that could constitute a “deemed export.”
ITAR does not prescribe a specific cybersecurity certification, but DDTC expects organizations to protect controlled data against unauthorized access, including cyberattacks. Best practice aligns ITAR controls with NIST SP 800-171 (for Controlled Unclassified Information) and, for DoD contractors, Cybersecurity Maturity Model Certification (CMMC).
CMMC
Having gotten three different companies to various CMMC statuses (Level 1, Level 2 certified, and Level 3) as well as consulting with countless other companies to their own CMMC certifications, I could write a blog series just about CMMC but for the sake of this article, I want to focus just on the main points:
If your company sells items to the US Government, and handles FCI and/or CUI and/or CDI then you’ll need CMMC.
So to begin, I would mention that CMMC is a maturity model certification, which has three levels.
Level 1 protects FCI (Federal Contract Information)
Level 2 protects CUI (Controlled Unclassified Information)
Level 3 protects CDI (Controlled Defense Information)
So you’ll have to start at Level 1 self assessed (14 controls), then move onto Level 2 self assessed (110 controls), and then finally you can move to Level 2 certified. Rarely will any company have to apply to Level 3 (CDI).
CMMC will require you to create an SSP (System Security Plan) to document your system(s), CUI boundary, detail controls, etc.As for a starting point, you’ll be defined as an OSC (Organization Seeking Certification) in the CMMC vernacular. In my experience the toughest portion to begin is how you’re going to structure your environment either Enclave (meaning you have a small, controlled subset of users/devices that have the CMMC controls) or Enterprise. Both structures have their strengths and weaknesses, and it will up to your Executive Team to decide which direction they’ll prefer. Once you have a rough draft, you should then review all of current software and hardware stack(s). Reviewing these stack(s) will also guide whether you need to change/upgrade software (Commercial vs Gov).
Once you have this, this is the basis of your plan and then you can start the process of moving towards CMMC Level 1. Once you reach Level 1, you’ll add this score in the PIEE site. You’ll then do the same with Level 2 self assessed, and then for Level 2 certified you’ll need a C3PAO to certify you. Typically the Level 2 certified process costs between $30,000 - $100,000 depending on the size of your company, enclave vs enterprise, etc).
Typically CMMC takes 12-24 months to achieve.
Additional Layers:
State and International Privacy Laws: CCPA/CPRA (California), GDPR (if serving EU customers), and emerging biometric or gun-owner data protections.
ATF Record-Keeping: While primarily paper/electronic Form 4473 rules, digital systems must maintain traceability and resist tampering.
The Canadian version of CMMC called, CPSCS (Canadian Program for Cyber Security Certification) begins Summer of 2026.
If you’re pursing CMMC and need to apply for CPSCS, make sure to apply via the United States /Canada Joint Certification Program as they will accept one certification for the other.
Upcoming Threat Vectors: What’s on the Horizon for 2026–2028
The firearm industry faces an accelerating threat landscape shaped by manufacturing digitization and geopolitics.
AI-Enhanced Attacks and Autonomous Ransomware: Adversaries now use AI for faster reconnaissance, polymorphic malware, and deepfake social engineering. Prompt-injection attacks against AI-assisted design tools or chat-based support systems could leak CAD files or proprietary manufacturing processes.
OT/ICS and IIoT Exposure: Smart factories connect CNC machines, robotic assembly, and inventory sensors to corporate networks. Legacy air-gapped systems are disappearing; ransomware groups already target uptime. A single compromised PLC can halt production or alter quality-control parameters.
Supply-Chain Poisoning and Third-Party Compromises: Software supply-chain attacks (e.g., SolarWinds-style) or compromised vendors (as in the Canadian mailing-service incident) will proliferate. Firearm manufacturers’ specialized suppliers are attractive secondary targets.
Nation-State Espionage and IP Theft: State actors (Iran, Russia, China) have incentives to steal firearm designs, suppress U.S. manufacturing, or harvest gun-owner data for intelligence or physical targeting. The 2025 Israeli gun-owner leak linked to Iranian hackers is a preview.
Insider Threats and Data Exfiltration: Disgruntled employees, contractors, or foreign-national staff with legitimate access remain a top risk under ITAR.
3D-Printing and Digital Blueprints: Proliferation of CAD files for firearms and accessories creates new vectors for theft or illegal distribution, blurring lines between manufacturing cybersecurity and export control.
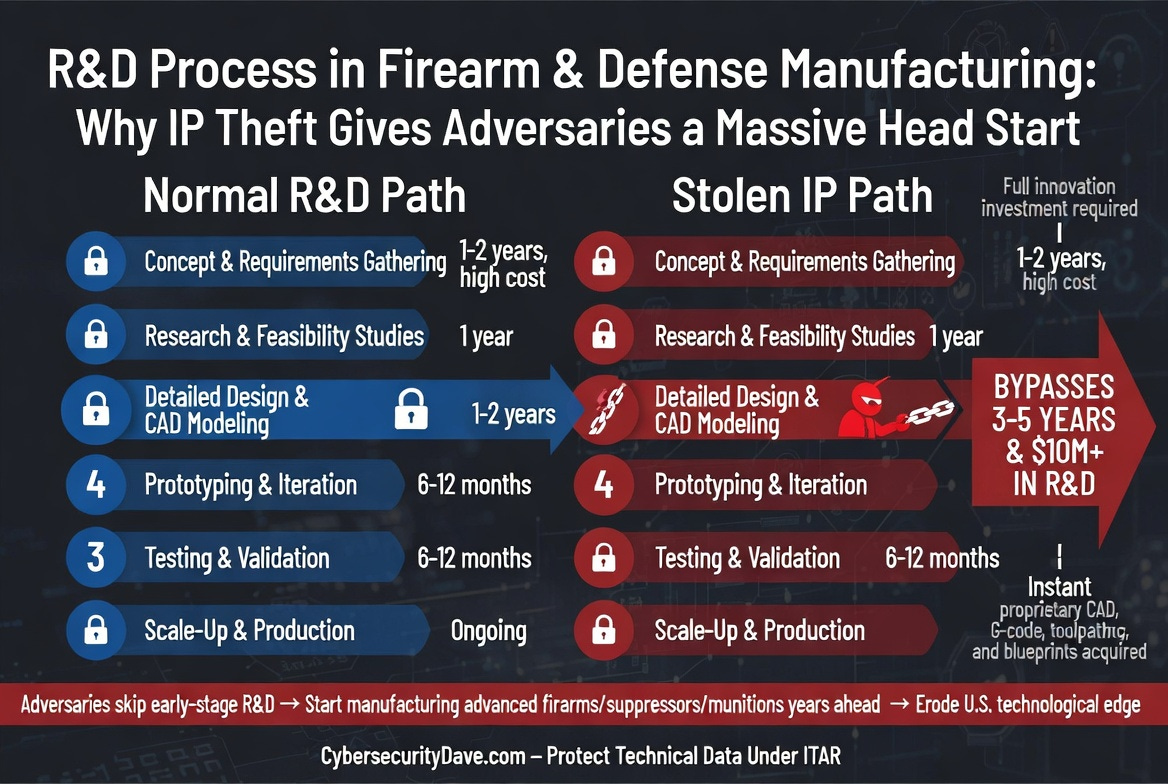
How IP theft works is when plans are stolen it allows malicious/bad actors to steal plans bypassing the development phase and start with prototyping phase, saving them money, and potentially even beating the original to the market.
Quantum and Long-Term Cryptographic Risks: While not immediate, quantum computing could break current encryption protecting technical data and customer databases—prompting a shift to post-quantum cryptography.
AI chat-bots: The rise of a plethora of AI chatbots might temp an employee to copy and paste sensitive items into one of the various platforms or LLMS
Vibe Coding: Vibe coding is inherently risky as it’s putting together code from various sources, other LLM’s, etc and can lead to a plethora of new vulnerabilities.
Moving Forward: Recommendations for Firearm Manufacturers
As I wrap this up, this article I wanted to finish with some final thoughts:
Adopt zero-trust architecture, network segmentation (IT vs. OT), and continuous monitoring
Tag all technical data at the very least
Vet third-party vendors rigorously and require flow-down ITAR clauses
Implement immutable backups, multi-factor authentication everywhere, and privileged-access management
Train staff on phishing, insider threats, and data-handling policies
Consider cyber insurance tailored to manufacturing and defense sectors
Engage with NSSF’s Project CyberSafe™ and industry ISACs for threat intelligence
Consider signing up for the FBI Infragard program for help with intelligence sharing
Cybersecurity is no longer optional for the firearm industry—it is a national-security, privacy, and business-continuity imperative. Past breaches show the cost of complacency; future threats demand proactive, defense-in-depth strategies.
Catch you all on the range.
Thank you all for reading this article. Feel free to comment, share or send me a private message: